Bluepurple Pulse: week ending October 22nd
When video game developer security and real-world attacks become a thing..
Welcome to the weekly highlights and analysis of the blueteamsec subreddit (and my wider reading). Not everything makes it in, but the best bits do.
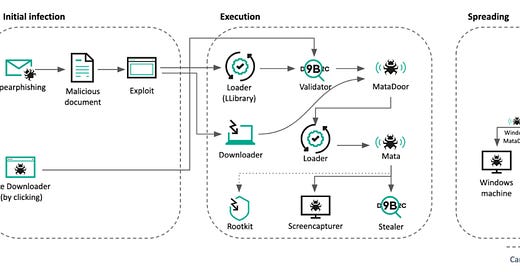
Operationally this week multiple developers had their Steam accounts compromised and the games backdoored resulting in Valve introducing mandatory SMS MFA in response. Then we had the rather large router compromise (see below).
In the high-level this week:
Secure-by-Design - we’ve gone big here - no turning back!
New Commander of the UK’s National Cyber Force appointed - Air Vice-Marshal Tim Neal-Hopes OBE has been appointed
UN cybercrime treaty: A menace in the making - article covering the below.
UN Cybercrime Treaty Talks End Without Consensus on Scope And Deep Divides About Surveillance Powers - It became apparent that many nations, including Russia, Eritrea, Burundi, Sierra Leone, Zimbabwe, Ghana, Korea, and others, were vying to expand the proposed treaty's surveillance scope to cover practically any offense imaginable where a computer wa…
Keep reading with a 7-day free trial
Subscribe to Cyber Defence Analysis for Blue & Purple Teams to keep reading this post and get 7 days of free access to the full post archives.